Generate SSH Key in Linux: How to Do It (Step-by-Step Guide)

Senior WebCoder
Secure Shell (SSH) is the most reliable way to connect to Linux servers. Traditionally, SSH uses passwords, but these are vulnerable to brute-force attacks. The safer approach is to generate SSH key in Linux, which allows password-less logins that are far harder to compromise.
In this guide, you’ll generate an SSH key pair, place the public key on your server, and configure your system to log in securely.
What You’ll Need
Before you start, make sure you have:
- A Linux system (Ubuntu, Debian, CentOS, Fedora, etc.)
- A user account with
sudoprivileges - Access to a remote server over SSH
💡Tip: Even if you don’t have a server, you can still practice by generating SSH keys locally and using them with GitHub, GitLab, or Bitbucket.
Step 1 — Check for Existing SSH Keys
It’s common for Linux systems to already have SSH keys. To check:
ls -al ~/.sshIf you see files like id_rsa.pub or id_ed25519.pub, then you already have a key. Otherwise, proceed to generate a new one.
Public keys (.pub) can be shared.
Private keys (without .pub) should never leave your machine.
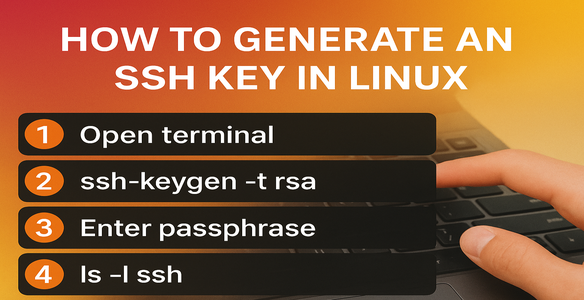
Step 2 —Generate SSH Key
Method 1: Default RSA Key (ssh-keygen)
The first step to enabling SSH key authentication is to generate a key pair on your local computer. This pair consists of:
- A private key → stays securely on your local machine.
- A public key → shared with the server to prove your identity.
Linux provides a utility called ssh-keygen (included in OpenSSH) that handles key generation.
By default, ssh-keygen generates a 3072-bit RSA key pair, though you can also choose Ed25519 or a stronger 4096-bit RSA key.
Generate Keys with ssh-keygen
ssh-keygenSample Output:
Generating public/private rsa key pair.
Enter file in which to save the key (/home/system-username/.ssh/id_rsa):
At this stage, you’re asked where to save the new keys. If you press ENTER, the utility stores them in the ~/.ssh folder in your home directory:
id_rsa→ private keyid_rsa.pub→ public key
💡 Best practice: Stick with the default path so SSH can automatically locate your keys later.
If an older key with the same name exists, you’ll see:
/home/system-username/.ssh/id_rsa already exists.
Overwrite (y/n)?
⚠️ Warning: If you choose y, the previous key will be deleted and you’ll no longer be able to use it for authentication. Only overwrite if you are certain you no longer need the old key.
Setting a Passphrase
Next, you’ll be asked to secure the private key with a passphrase:
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
- If you enter a passphrase, the key file on your computer will be encrypted.
- If you leave it empty, SSH will allow password-less logins without asking for extra confirmation.
Why Add a Passphrase?
Even though SSH keys are already secure, a passphrase adds another layer of protection:
- The private key is never transmitted across the network, only stored locally.
- The
.sshdirectory and key files have strict file permissions so other users cannot access them. - If an attacker gains access to your local system, the passphrase prevents immediate use of the key, giving you time to revoke it and generate a new pair.
💡 While optional, it’s strongly recommended to set a passphrase for maximum security.
Final Confirmation
Once complete, you’ll see something like:
Your identification has been saved in /home/system-username/.ssh/id_rsa.
Your public key has been saved in /home/system-username/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:CAjsV9M/tt5skazroTc1ZRGCBz+kGtYUIPhRvvZJYBs system-username@hostname
The key's randomart image is:
+---[RSA 3072]----+
|o ..oo.++o .. |
| o o +o.o.+... |
|. . + oE.o.o . |
| . . oo.B+ .o |
| . .=S.+ + |
| . o..* |
| .+= o |
| .=.+ |
| .oo+ |
+----[SHA256]-----+
This message confirms your new key pair is ready. The fingerprint is a unique identifier, and the randomart graphic is a visual aid that helps verify authenticity.
Method 2: Recommended Ed25519 Key
ssh-keygen -t ed25519 -C "[email protected]"-t ed25519→ sets the key type-C→ adds a label (commonly your email)
If Ed25519 is unsupported, fall back to RSA:
ssh-keygen -t rsa -b 4096 -C "[email protected]"Sample Interactive Output
Generating public/private ed25519 key pair.
Enter file in which to save the key (/home/system-username/.ssh/id_ed25519):
Press ENTER to accept the default location.
Next prompt:
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
- With a passphrase → adds an extra layer of protection
- Without → faster login, but less secure
Once complete, you’ll see:
Your identification has been saved in /home/system-username/.ssh/id_ed25519
Your public key has been saved in /home/system-username/.ssh/id_ed25519.pub
Now we successfully generated your SSH key pair.
Step 3 — View and Confirm Keys
List your .ssh directory:
ls ~/.sshExpected output:
id_ed25519 id_ed25519.pub known_hosts
id_ed25519→ private key (keep secret)id_ed25519.pub→ public key (safe to share)
Step 4 — Copy SSH Key to Server
To log in with keys, you need to add your public key to the server.
The easiest method:
ssh-copy-id system-username@server_ipIf not available, copy manually:
cat ~/.ssh/id_ed25519.pubLog into your server and paste the key into:
~/.ssh/authorized_keysSave and exit.
Step 5 — Test SSH Authentication
Now test:
ssh system-username@server_ipIf configured correctly, you’ll log in without typing a password.
If you set a passphrase, you’ll enter it once per session.
Step 6 — (Optional) Use SSH Agent
If your key has a passphrase, you can use ssh-agent to avoid typing it repeatedly.
Start the agent:
eval "$(ssh-agent -s)"Add your key:
ssh-add ~/.ssh/id_ed25519Now your key is cached for the session.
Conclusion
You’ve learned how to generate SSH key in Linux, confirm it, copy it to your server, and use it for secure logins.
SSH keys are:
- Safer than passwords
- Easier for automation
- Widely supported (Git, servers, cloud providers)
Next steps:
- Set up fail2ban or firewalls for extra security
- Use keys for Git hosting services
- Generate multiple keys for different environments

Abinesh S
Senior WebCoder
Senior WebCoder at FUEiNT, specializing in advanced frontend architecture, Next.js, and performance optimization. Passionate about determining the best tools for the job.
